Hydra
Penetration Testing Tools
You are here: Home » Password Attacks » Hydra
Hydra Description
A very fast network logon cracker which support many different services.
Currently this tool supports the following protocols: Asterisk, AFP, Cisco AAA, Cisco auth, Cisco enable, CVS, Firebird, FTP, HTTP-FORM-GET, HTTP-FORM-POST, HTTP-GET, HTTP-HEAD, HTTP-POST, HTTP-PROXY, HTTPS-FORM-GET, HTTPS-FORM-POST, HTTPS-GET, HTTPS-HEAD, HTTPS-POST, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MYSQL, NCP, NNTP, Oracle Listener, Oracle SID, Oracle, PC-Anywhere, PCNFS, POP3, POSTGRES, RDP, Rexec, Rlogin, Rsh, RTSP, SAP/R3, SIP, SMB, SMTP, SMTP Enum, SNMP v1+v2+v3, SOCKS5, SSH (v1 and v2), SSHKEY, Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
Homepage: https://www.thc.org/thc-hydra/
Author: Van Hauser, Roland Kessler
License: AGPL-3.0
Hydra Help
Syntax:
| 1 | hydra [[[-l LOGIN|-L FILE] [-p PASS|-P FILE]] | [-C FILE]] [-e nsr] [-o FILE] [-t TASKS] [-M FILE [-T TASKS]] [-w TIME] [-W TIME] [-f] [-s PORT] [-x MIN:MAX:CHARSET] [-SOuvVd46] [service://server[:PORT][/OPT]] |
Options:
| 12345678910111213141516171819202122232425262728 | -R restore a previous aborted/crashed session-S perform an SSL connect-s PORT if the service is on a different default port, define it here-l LOGIN or -L FILE login with LOGIN name, or load several logins from FILE-p PASS or -P FILE try password PASS, or load several passwords from FILE-x MIN:MAX:CHARSET password bruteforce generation, type "-x -h" to get help-e nsr try "n" null password, "s" login as pass and/or "r" reversed login-u loop around users, not passwords (effective! implied with -x)-C FILE colon separated "login:pass" format, instead of -L/-P options-M FILE list of servers to attack, one entry per line, ':' to specify port-o FILE write found login/password pairs to FILE instead of stdout-f / -F exit when a login/pass pair is found (-M: -f per host, -F global)-t TASKS run TASKS number of connects in parallel (per host, default: 16)-w / -W TIME waittime for responses (32) / between connects per thread (0)-4 / -6 use IPv4 (default) / IPv6 addresses (put always in [] also in -M)-v / -V / -d verbose mode / show login+pass for each attempt / debug mode -O use old SSL v2 and v3-q do not print messages about connection errors-U service module usage detailsserver the target: DNS, IP or 192.168.0.0/24 (this OR the -M option)service the service to crack (see below for supported protocols)OPT some service modules support additional input (-U for module help) Use HYDRA_PROXY_HTTP or HYDRA_PROXY - and if needed HYDRA_PROXY_AUTH - environment for a proxy setup.E.g.: % export HYDRA_PROXY=socks5://127.0.0.1:9150 (or socks4:// or connect://)% export HYDRA_PROXY_HTTP=http://proxy:8080% export HYDRA_PROXY_AUTH=user:pass |
Hydra bruteforce password generation option usage:
| 12345678 | -x MIN:MAX:CHARSET MIN is the minimum number of characters in the passwordMAX is the maximum number of characters in the passwordCHARSET is a specification of the characters to use in the generationvalid CHARSET values are: 'a' for lowercase letters,'A' for uppercase letters, '1' for numbers, and for all others,just add their real representation. |
Examples:
| 1234 | -x 3:5:a generate passwords from length 3 to 5 with all lowercase letters-x 5:8:A1 generate passwords from length 5 to 8 with uppercase and numbers-x 1:3:/ generate passwords from length 1 to 3 containing only slashes-x 5:5:/%,.- generate passwords with length 5 which consists only of /%,.- |
Hydra Supported Protocols
Supported protocols:
- asterisk
- afp
- cisco
- cisco-enable
- cvs
- firebird
- ftp
- ftps
- http-head
- https-head
- http-get
- https-get
- http-post
- https-post
- http-get-form
- https-get-form
- http-post-form
- https-post-form
- http-proxy
- http-proxy-urlenum
- icq
- imap
- imaps
- irc
- ldap2
- ldap2s
- ldap3
- ldap3s
- ldap3-crammd5
- ldap3-crammd5s
- ldap3-digestmd5
- ldap3-digestmd5s
- mssql
- mysql
- nntp
- oracle-listener
- oracle-sid
- pcanywhere
- pcnfs
- pop3
- pop3s
- postgres
- rdp
- redis
- rexec
- rlogin
- rsh
- rtsp
- s7-300
- sip
- smb
- smtp
- smtps
- smtp-enum
- snmp
- socks5
- ssh
- sshkey
- svn
- teamspeak
- telnet
- telnets
- vmauthd
- vnc
- xmpp
Options of Hydra Supported protocols
cisco
Module cisco is optionally taking the keyword ENTER, it then sends an initial ENTER when connecting to the service.
cisco-enable
Module cisco-enable is optionally taking the logon password for the cisco device
Note: if AAA authentication is used, use the -l option for the username and the optional parameter for the password of the user.
Examples:
| 123 | hydra -P pass.txt target cisco-enable (direct console access)hydra -P pass.txt -m cisco target cisco-enable (Logon password cisco)hydra -l foo -m bar -P pass.txt target cisco-enable (AAA Login foo, password bar) |
cvs
Module cvs is optionally taking the repository name to attack, default is "/root"
firebird
Module firebird is optionally taking the database path to attack, default is "C:\Program Files\Firebird\Firebird_1_5\security.fdb"
http-get, https-get, http-post, https-post
Module http-get requires the page to authenticate.
For example: "/secret" or "http://bla.com/foo/bar" or "https://test.com:8080/members"
http-get-form, https-get-form, http-post-form, https-post-form
Module http-get-form requires the page and the parameters for the web form.
By default this module is configured to follow a maximum of 5 redirections in a row. It always gathers a new cookie from the same URL without variables The parameters take three ":" separated values, plus optional values.
(Note: if you need a colon in the option string as value, escape it with "\:", but do not escape a "\" with "\\".)
Syntax:
| 1 | <url>:<form parameters>:<condition string>[:<optional>[:<optional>]</optional></optional> |
- First is the page on the server to GET or POST to (URL).
- Second is the POST/GET variables (taken from either the browser, proxy, etc. with usernames and passwords being replaced in the "^USER^" and "^PASS^" placeholders (FORM PARAMETERS)
- Third is the string that it checks for an *invalid* login (by default). Invalid condition login check can be preceded by "F=", successful condition login check must be preceded by "S=". This is where most people get it wrong. You have to check the webapp what a failed string looks like and put it in this parameter!
The following parameters are optional:
C=/page/uri
to define a different page to gather initial cookies from
(h|H)=My-Hdr\: foo
to send a user defined HTTP header with each request
^USER^ and ^PASS^ can also be put into these headers!
Note: 'h' will add the user-defined header at the end regardless it's already being sent by Hydra or not.
'H' will replace the value of that header if it exists, by the one supplied by the user, or add the header at the end.
Note that if you are going to put colons (:) in your headers you should escape them with a backslash (\). All colons that are not option separators should be escaped (see the examples above and below).
You can specify a header without escaping the colons, but that way you will not be able to put colons in the header value itself, as they will be interpreted by hydra as option separators.
Examples:
| 12345 | "/login.php:user=^USER^&pass=^PASS^:incorrect""/login.php:user=^USER^&pass=^PASS^&colon=colon\:escape:S=authlog=.*success""/login.php:user=^USER^&pass=^PASS^&mid=123:authlog=.*failed""/:user=^USER&pass=^PASS^:failed:H=Authorization\: Basic dT1w:H=Cookie\: sessid=aaaa:h=X-User\: ^USER^""/exchweb/bin/auth/owaauth.dll:destination=http%3A%2F%2F<target>%2Fexchange&flags=0&username=<domain>%5C^USER^&password=^PASS^&SubmitCreds=x&trusted=0:reason=:C=/exchweb" |
http-proxy
Module http-proxy is optionally taking the page to authenticate at.
Default is http://www.microsoft.com/)
Basic, DIGEST-MD5 and NTLM are supported and negotiated automatically.
http-proxy-urlenum
Module http-proxy-urlenum only uses the -L option, not -x or -p/-P option. The -L loginfile must contain the URL list to try through the proxy. The proxy credentials cann be put as the optional parameter, e.g.
| 12 | hydra -L urllist.txt -s 3128 target.com http-proxy-urlenum user:passhydra -L urllist.txt http-proxy-urlenum://target.com:3128/user:pass |
imap, imaps
Module imap is optionally taking one authentication type of: CLEAR or APOP (default), LOGIN, PLAIN, CRAM-MD5, CRAM-SHA1, CRAM-SHA256, DIGEST-MD5, NTLM
Additionally TLS encryption via STARTTLS can be enforced with the TLS option.
Example: imap://target/TLS:PLAIN
irc
Module irc is optionally taking the general server password, if the server is requiring one and none is passed the password from -p/-P will be used
ldap2, ldap2s, ldap3, ldap3s, ldap3-crammd5, ldap3-crammd5s, ldap3-digestmd5, ldap3-digestmd5s
Module ldap2 is optionally taking the DN (depending of the auth method choosed
Note: you can also specify the DN as login when Simple auth method is used).
The keyword "^USER^" is replaced with the login.
Special notes for Simple method has 3 operation modes: anonymous, (no user no pass), unauthenticated (user but no pass), user/pass authenticated (user and pass).
So don't forget to set empty string as user/pass to test all modes.
Hint: to authenticate to a windows active directy ldap, this is usually cn=^USER^,cn=users,dc=foo,dc=bar,dc=com for domain foo.bar.com
mysql
Module mysql is optionally taking the database to attack, default is "mysql"
nntp
Module nntp is optionally taking one authentication type of: USER (default), LOGIN, PLAIN, CRAM-MD5, DIGEST-MD5, NTLM
oracle-listener
Module oracle-listener / tns is optionally taking the mode the password is stored as, could be PLAIN (default) or CLEAR
pop3, pop3s
Module pop3 is optionally taking one authentication type of: CLEAR (default), LOGIN, PLAIN, CRAM-MD5, CRAM-SHA1, CRAM-SHA256, DIGEST-MD5, NTLM.
Additionally TLS encryption via STLS can be enforced with the TLS option.
Example: pop3://target/TLS:PLAIN
postgres
Module postgres is optionally taking the database to attack, default is "template1"
rdp
Module rdp is optionally taking the windows domain name.
For example:
| 1 | hydra rdp://192.168.0.1/firstdomainname -l john -p doe |
s7-300
Module S7-300 is for a special Siemens PLC. It either requires only a password or no authentication, so just use the -p or -P option.
smb
Module smb default value is set to test both local and domain account, using a simple password with NTLM dialect.
Note: you can set the group type using LOCAL or DOMAIN keyword or other_domain:{value} to specify a trusted domain.
You can set the password type using HASH or MACHINE keyword (to use the Machine's NetBIOS name as the password).
You can set the dialect using NTLMV2, NTLM, LMV2, LM keyword.
Example:
| 123 | hydra smb://microsoft.com -l admin -p tooeasy -m "local lmv2"hydra smb://microsoft.com -l admin -p D5731CFC6C2A069C21FD0D49CAEBC9EA:2126EE7712D37E265FD63F2C84D2B13D::: -m "local hash"hydra smb://microsoft.com -l admin -p tooeasy -m "other_domain:SECONDDOMAIN" |
smtp, smtps
Module smtp is optionally taking one authentication type of: LOGIN (default), PLAIN, CRAM-MD5, DIGEST-MD5, NTLM
Additionally TLS encryption via STARTTLS can be enforced with the TLS option.
Example: smtp://target/TLS:PLAIN
smtp-enum
Module smtp-enum is optionally taking one SMTP command of: VRFY (default), EXPN, RCPT (which will connect using "root" account) login parameter is used as username and password parameter as the domain name
For example to test if john@localhost exists on 192.168.0.1:
| 1 | hydra smtp-enum://192.168.0.1/vrfy -l john -p localhost |
snmp
Module snmp is optionally taking the following parameters:
| 12345678910111213 | READ perform read requests (default)WRITE perform write requests1 use SNMP version 1 (default)2 use SNMP version 23 use SNMP version 3Note that SNMP version 3 usually uses both login and passwords!SNMP version 3 has the following optional sub parameters:MD5 use MD5 authentication (default)SHA use SHA authenticationDES use DES encryptionAES use AES encryptionif no -p/-P parameter is given, SNMPv3 noauth is performed, whichonly requires a password (or username) not both. |
To combine the options, use colons (":"), e.g.:
| 12 | hydra -L user.txt -P pass.txt -m 3:SHA:AES:READ target.com snmphydra -P pass.txt -m 2 target.com snmp |
sshkey
Module sshkey does not provide additional options, although the semantic for options -p and -P is changed:
- -p expects a path to an unencrypted private key in PEM format.
- -P expects a filename containing a list of path to some unencrypted private keys in PEM format.
svn
Module svn is optionally taking the repository name to attack, default is "trunk"
telnet, telnets
Module telnet is optionally taking the string which is displayed after a successful login (case insensitive), use if the default in the telnet module produces too many false positives
xmpp
Module xmpp is optionally taking one authentication type of: LOGIN (default), PLAIN, CRAM-MD5, DIGEST-MD5, SCRAM-SHA1
Note, the target passed should be a fdqn as the value is used in the Jabber init request, example: hermes.jabber.org
Hydra Usage Example
Attempt to login as the root user (-l root) using a password list (-P /usr/share/wordlists/metasploit/unix_passwords.txt) with 6 threads (-t 6) on the given SSH server (ssh://192.168.1.123):
| 123456 | hydra -l root -P /usr/share/wordlists/metasploit/unix_passwords.txt -t 6 ssh://192.168.1.123Hydra v7.6 (c)2013 by van Hauser/THC & David Maciejak - for legal purposes only Hydra (http://www.thc.org/thc-hydra) starting at 2014-05-19 07:53:33[DATA] 6 tasks, 1 server, 1003 login tries (l:1/p:1003), ~167 tries per task[DATA] attacking service ssh on port 22 |
Attempt to login as the user (-l user) using a password list (-P passlist.txt) on the given FTP server (ftp://192.168.0.1):
| 1 | hydra -l user -P passlist.txt ftp://192.168.0.1 |
Attempt to login on the given SSH servers (ssh) from the list (-M targets.txt) using a user list (-L logins.txt) and password list (-P pws.txt):
| 1 | hydra -L logins.txt -P pws.txt -M targets.txt ssh |
Attempt to login on the given FTP servers on the given subnet (ftp://[192.168.0.0/24]/) as the user admin (-l admin) and the password password (-p password):
| 1 | hydra -l admin -p password ftp://[192.168.0.0/24]/ |
Attempt to login on the given mail server (imap://192.168.0.1/), using IMAP protocol with a user list (-L userlist.txt) and the password defaultpw (-p defaultpw), taking the authentication type PLAIN:
| 1 | hydra -L userlist.txt -p defaultpw imap://192.168.0.1/PLAIN |
Attempt to login on the given mail server using POP3S on the given IPv6 (-6) address 2001:db8::1, on port 143 using the credential list "login:password" from the defaults.txt file (-C defaults.txt) taking the authentication type DIGEST-MD5 and enforced TLS encryption via STLS (TLS).
| 1 | hydra -C defaults.txt -6 pop3s://[2001:db8::1]:143/TLS:DIGEST-MD5 |
xHydra (GUI for THC-Hydra)
xhydra is Gtk+2 frontend for thc-hydra.
To start xHydra GUI issue:
| 1 | xhydra |
Tools included in the hydra package
- hydra – Very fast network logon cracker
- pw-inspector – Reads passwords in and prints those which meet the requirements
Help pw-inspector
PW-Inspector reads passwords in and prints those which meet the requirements. The return code is the number of valid passwords found, 0 if none was found. Use for security: check passwords, if 0 is returned, reject password choice.
Use for hacking: trim your dictionary file to the pw requirements of the target.
Syntax:
| 1 | pw-inspector [-i FILE] [-o FILE] [-m MINLEN] [-M MAXLEN] [-c MINSETS] -l -u -n -p -s |
| 123456789101112 | Options:-i FILE file to read passwords from (default: stdin)-o FILE file to write valid passwords to (default: stdout)-m MINLEN minimum length of a valid password-M MAXLEN maximum length of a valid password-c MINSETS the minimum number of sets required (default: all given)Sets:-l lowcase characters (a,b,c,d, etc.)-u upcase characters (A,B,C,D, etc.)-n numbers (1,2,3,4, etc.)-p printable characters (which are not -l/-n/-p, e.g. $,!,/,(,*, etc.)-s special characters - all others not withint the sets above |
How to install Hydra
The program is pre-installed on Kali Linux.
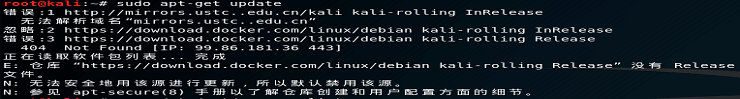
Installation on Linux (Debian, Mint, Ubuntu)
| 1234567 | sudo apt-get remove hydrasudo apt-get install libssl-dev libssh-dev libidn11-dev libpcre3-dev libgtk2.0-dev libmysqlclient-dev libpq-dev libsvn-dev firebird2.1-dev libncp-devgit clone https://github.com/vanhauser-thc/thc-hydra.gitcd thc-hydra/./configuremakesudo make install |
Hydra Screenshots




Hydra Tutorials
Coming soon…
Related tools
- patator (97.6%)
- oclHashcat (53%)
- hashcat (Hashcat & oclHashcat) (53%)
- Medusa (53%)
- Maltego (52.4%)
- evilginx2 (RANDOM - 1.1%)
Tags: Brute-force attack gui mssql mysql oracle passwords postgresql SMB SNMP THC-Hydra
You May Also Like
Medusa
Crunch
ALSO RECOMMENDED:
RECENT POSTS
CATEGORIES
- Anonymity
- Digital forensics
- Exploitation Tools
- Hardware Hacking
- Information Gathering
- Maintaining Access
- Password Attacks
- Sniffing & Spoofing
- Stress Testing
- Vulnerability Analysis
- Web Applications
- Wireless Attacks
GUIDES AND ARTICLES
- VNC Security AuditSource: Ethical hacking and penetration testing Published on 2020-06-09
- How to protect web server on Kali Linux from unauthorized accessSource: Ethical hacking and penetration testing Published on 2020-06-04
- How to crack VNC password from captured traffic (challenge response)Source: Ethical hacking and penetration testing Published on 2020-06-03
- Linux Wi-Fi Cheat Sheet: Tips and TroubleshootingSource: Ethical hacking and penetration testing Published on 2020-05-28
- Linux kernel modulesSource: Ethical hacking and penetration testing Published on 2020-05-27
© 2020 Penetration Testing Tools. All Rights Reserved.Wiles
 admin
admin