使用NMAP无法在网络中检测到我的Android手机
nmap 主要用于
1,Host discovery (主机发现)
2,Service /version detection(服务于版本检测)
3,Operating system detection(操作系统检测)
4,Network traceroute(网络追踪)
5,Nmap Scripting Engine(nmap脚本检测)
我想找到使用我的WiFi连接的所有设备。
工具使用
一,nmap -sn 91.169.99.1-254 网段扫描
TCP/UDP扫描方式
TCP SYN扫描 nmap -sS 01.1.169.99.1
TCP Connect扫描 nmap -sT 01.1.169.99.1
TCP FIN扫描 nmap -sF 01.1.169.99.1
UDP扫描 nmap -sU 01.1.169.99.1 (扫描时间长,效果不好,路由器限速)
下一步端口服务版本检测 nmap -sV 91.169.99.1 (速度慢 ,-A更慢)
我用了:
牛牛牛 针对法国电信的网络猫freebox开发端口
root@kali:~# nmap -sS -p 1-65535 -v 91.169.99.1 -Pn
Host is up (0.027s latency).
Not shown: 65531 filtered ports
PORT STATE SERVICE
33397/tcp closed unknown
33839/tcp open unknown
40786/tcp open unknown
44261/tcp open unknown
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 2631.09 seconds
Raw packets sent: 131135 (5.770MB) | Rcvd: 102 (4.496KB)
通过详细分析nmap -A 91.169.99.1 -p49247,62835 -Pn
得到PORT STATE SERVICE VERSION
49247/tcp open http nginx
| http-robots.txt: 1 disallowed entry
|_/
| http-title: Freebox OS :: Identification
|Requested resource was /login.php
62835/tcp open ssl/http nginx
| http-robots.txt: 1 disallowed entry
|/
| http-title: 400 The plain HTTP request was sent to HTTPS port
|_Requested resource was /login.php
| ssl-cert: Subject: commonName=ikizwo4q.fbxos.fr/countryName=FR (对应的ipv6地址DNS域名地址通过远程访问ikizwo4q.fbxos.fr:49247远程管理入口login.php 可惜没激活)
| Subject Alternative Name: DNS:ikizwo4q.fbxos.fr, DNS:mafreebox.freebox.fr, DNS:mafreebox6.freebox.fr
| Not valid before: 2021-01-19T02:37:02
|_Not valid after: 2021-04-19T02:42:02
|ssl-date: TLS randomness does not represent time
| tls-alpn:
| http/1.1
| tls-nextprotoneg:
|_ http/1.1
尝试使用:routersploit搞一下
https://github.com/reverse-shell/routersploit
autopwn模块,可以自动检查适合我们设置的目标的任何漏洞
search autopwn
use scanners/autopwn
set threads 20
set tartget 91.169.99.1
run
nmap -vv -sP 192.168.1.1-100
我可以找到我的本地PC和路由器,但是我无法使用此命令检测到我的Android手机。
网络:
192.168.1.20 router
192.168.1.34 local pc
192.168.1.33 Android phone
NMAP:
user@Internetcafe-PC12:~$ nmap -vv -sP 192.168.1.1-100
Starting Nmap 5.21 ( http://nmap.org ) at 2017-06-25 12:40 IST
Initiating Ping Scan at 12:40
Scanning 100 hosts [2 ports/host]
Completed Ping Scan at 12:40, 2.71s elapsed (100 total hosts)
Initiating Parallel DNS resolution of 100 hosts. at 12:40
Completed Parallel DNS resolution of 100 hosts. at 12:40, 0.31s elapsed
Nmap scan report for 192.168.1.1 [host down]
Nmap scan report for 192.168.1.19 [host down]
Nmap scan report for 192.168.1.20
Host is up (0.0029s latency).
Nmap scan report for 192.168.1.32 [host down]
Nmap scan report for 192.168.1.33 [host down]
Nmap scan report for 192.168.1.34
Host is up (0.00021s latency).
Nmap scan report for 192.168.1.35 [host down]
Nmap scan report for 192.168.1.36 [host down]
Nmap done: 100 IP addresses (2 hosts up) scanned in 3.02 seconds
user@Internetcafe-PC12:~$ ping 192.168.1.33
PING 192.168.1.33 (192.168.1.33) 56(84) bytes of data.
64 bytes from 192.168.1.33: icmp_req=1 ttl=64 time=121 ms
64 bytes from 192.168.1.33: icmp_req=2 ttl=64 time=47.1 ms
networking wireless-networking ubuntu-12.04 nmap
— JAAY
source
Answers:
nmap -A -T4 37.164.237.241 -sU -P0
在Nmap上尝试使用其他修改器以避免“ping扫描”:
nmap -sS -sV -vv -n -Pn -T4 192.168.1.1-100
nmap -vv -A -n 192.168.1.1-100
你也可以添加 sudo 之前 nmap,只是为了确保你获得所有特权。
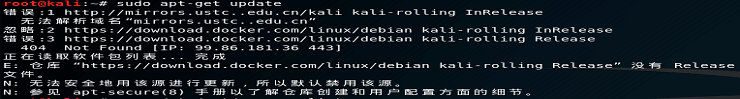
root@kali:~# nmap -vv -sP 91.169.99.1-100
Warning: The -sP option is deprecated. Please use -sn
Starting Nmap 7.80 ( https://nmap.org ) at 2021-02-19 22:24 UTC
Initiating Ping Scan at 22:24
Scanning 100 hosts [4 ports/host]
Ping Scan Timing: About 37.62% done; ETC: 22:25 (0:00:51 remaining)
Completed Ping Scan at 22:25, 81.98s elapsed (100 total hosts)
Nmap scan report for 91.169.99.1 [host down, received no-response]
Nmap scan report for 91.169.99.2 [host down, received no-response]
Nmap scan report for 91.169.99.3 [host down, received no-response]
Nmap scan report for 91.169.99.4 [host down, received no-response]
Nmap scan report for 91.169.99.5 [host down, received no-response]
Nmap scan report for 91.169.99.6 [host down, received no-response]
Nmap scan report for 91.169.99.7 [host down, received no-response]
Nmap scan report for 91.169.99.8 [host down, received no-response]
Nmap scan report for 91.169.99.9 [host down, received no-response]
修改扫描方式
root@kali:~# nmap -vv -sn 91.169.99.1-100 (无效)
更改扫描方式
nmap -vv -sS 91.169.99.1 -Pn (有效)
nc -z -v -w 1 192.168.0.171 80
跟踪路由
nmap -A -T4 91.169.99.1-100 -Pn
无ping扫描
sudo nmap 91.169.99.3 -sU -P0
最后使用杀手锏扫描
root@kali:~# sudo nmap 91.169.99.1 -sU -P0
Starting Nmap 7.80 ( https://nmap.org ) at 2021-02-19 23:05 UTC
Nmap scan report for 91-169-99-1.subs.proxad.net (91.169.99.1)
Host is up (0.022s latency).
Not shown: 997 open|filtered ports
PORT STATE SERVICE
9/udp closed discard
67/udp closed dhcps
68/udp closed dhcpc
sudo nmap 91.169.99.1 -sS -sU -P0
扫描手机ip跟踪路由
21 16.98 ms be5341.rcr21.b032899-0.par01.atlas.cogentco.com (149.6.115.73)
22 20.14 ms be2922.ccr42.par01.atlas.cogentco.com (130.117.1.161)
23 20.11 ms be3518.agr21.par01.atlas.cogentco.com (130.117.50.42)
24 20.10 ms 149.14.152.218
25 20.10 ms 194.149.166.57
26 17.05 ms ppp3-metz.isdnet.net (194.149.166.130)
27 20.59 ms ppp23-metz.isdnet.net (194.149.166.150)
再搞一下
nmap -sS -p 1-65535 -v 91.169.99.1 -Pn
使用其他工具扫描nping的echo mode
nping --echo-client "public" 91.169.99.1 --tcp -p1-50 --flags ack
root@kali:~#
root@kali:~# nping -c 1 -p 22 91.169.99.3 --tcp
Starting Nping 0.7.80 ( https://nmap.org/nping ) at 2021-02-20 14:15 UTC
SENT (0.0379s) TCP 10.10.244.245:11655 > 91.169.99.3:22 S ttl=64 id=12813 iplen=40 seq=899627076 win=1480
Max rtt: N/A | Min rtt: N/A | Avg rtt: N/A
Raw packets sent: 1 (40B) | Rcvd: 0 (0B) | Lost: 1 (100.00%)
Nping done: 1 IP address pinged in 1.07 seconds
测试网段
root@kali:~# nping -c 1 -p 22 91.169.99.1-254 --tcp
Starting Nping 0.7.80 ( https://nmap.org/nping ) at 2021-02-20 14:15 UTC
SENT (0.0484s) TCP 10.10.244.245:39684 > 91.169.99.1:22 S ttl=64 id=36158 iplen=40 seq=173977425 win=1480
SENT (1.0485s) TCP 10.10.244.245:39684 > 91.169.99.2:22 S ttl=64 id=36158 iplen=40 seq=173977425 win=1480
ttl=64 表示Linux系统
使用其他工具nbtscan 91.169.99.1 (针对windows平台比较实用
)_
nmap参数参考
-sT TCP connect()扫描,这种方式会在目标主机的日志中会记录大批的连接请求以及错误信息
-sS 半开扫描,很少有系统能够把这记入系统日志。不过,需要root权限
-sF -sN 秘密FIN数据包扫描、圣诞树(Xmas Tree)、空(Null)扫描模式
-sP ping扫描,Nmap在扫描端口时,默认都会使用ping扫描,只有主机存活,Nmap才会继续扫描
-sU UDP扫描,但UDP扫描是不可靠的
-sA 这项高级的扫描方法通常用来穿过防火墙的规则集
-sV探测端口服务版本
-P0 扫描之前不需要ping,有些防火墙禁止ping。可以使用此选项进行扫描
-v显示扫描过程,推荐使用
-h 帮助选项,必看,最清楚的帮助文档
-p 指定端口,如[1-65535],[1433,135,3389,22]等格式
-O 启用远程操作系统检测,存在误报
-A 全面系统检测,启用脚本检测,扫描等。
-oN/-oX/-oG 讲将报告写入文件,分别是三种格式[正常,XML,grepable]
-T4 针对TCP端口禁止动态扫描延迟超过10ms
-iL 读取主机列表,例如[-iL C:\ip.txt]
 admin
admin